Configure SSL to securely connect to Azure Database for MySQL
Azure DB for MySQL supports connecting to client applications using SSL. Enforcing SSL between your database server and your client apps will protect against “man in the middle” attacks by encrypting the data stream between the server and your application.
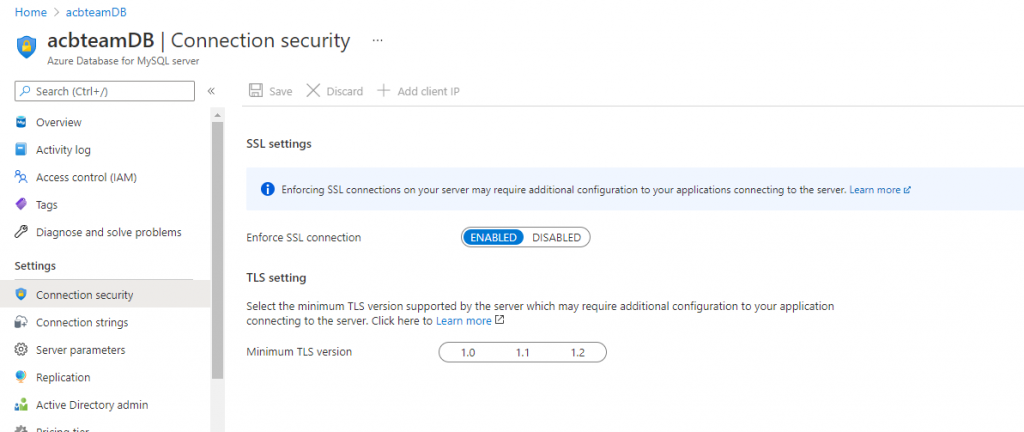
First we are going to Enable SSL connection in Azure MYSQL Dashboard > Connection Security
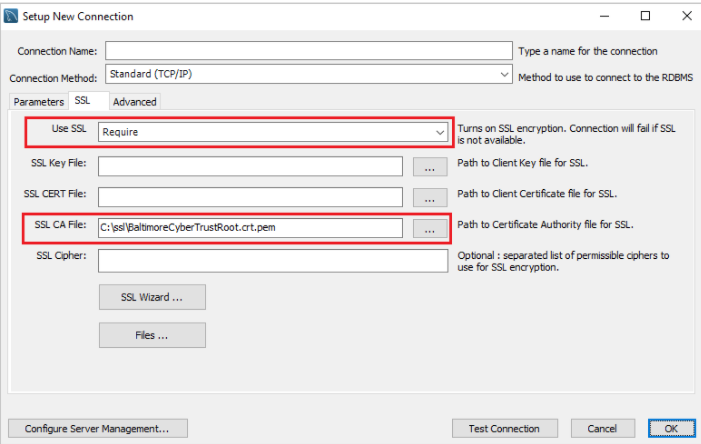
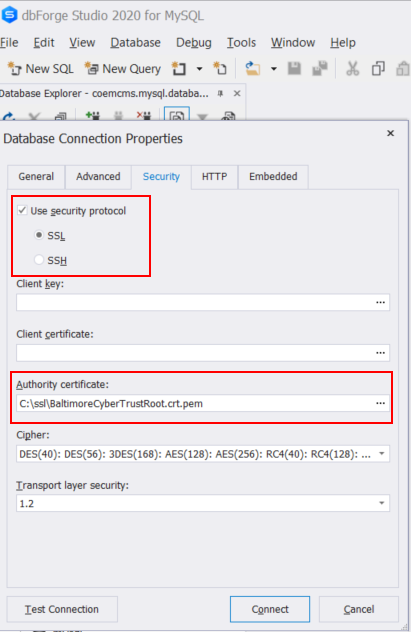
Once we have our SSL enabled we need to download the certificate needed to communicate over SSL with your Azure Database for MySQL from https://www.digicert.com/CACerts/BaltimoreCyberTrustRoot.crt.pem and save the certificate file to your local.
Then we are going to show some examples of how to connect with our clients:
Configure MySQL Workbench to connect over SSL
Configure DBForge Studio MySQL to connect over SSL
Configure a Database Backup .bat script (using mysqldump) and compress file to a .rar:
- We set the current date for scheduling the .bat file on Windows Task Scheduler.
- In the mysqldump sentence, we have to add our credentials: User, Password, Host, DBName, Cert.pem local path where we saved our server certificate and ssl-mode required
- The last sentence compress MySQL backup into a rar file (WinRAR needs to be installed)
Set currentdate=%date:~6,4%%date:~3,2%%date:~0,2%
"C:\Program Files\MySQL\MySQL Server 5.6\bin\mysqldump.exe" --user=user@acbteam --password=mypassword --ssl-mode=REQUIRED --ssl-ca=C:\ssl\BaltimoreCyberTrustRoot.crt.pem --host=acbteam.database.azure.com dbname > C:\backup\dbname.%currentdate%.sql
rar a C:\backup\%currentdate%.rar C:\backup\dbname.%currentdate%.sql
del C:\backup\dbname.%currentdate%.sql
DC
Related Articles That Might
Interest You

ASP Net Core Service Lifetime

Configure SSL to securely connect to Azure Database for MySQL

Leave a Reply